Sunday, November 29, 2009
Integration Services Videos (SQL Server 2008)
Friday, November 27, 2009
How to create a computed column using SQL Server Management Studio?
Take the following steps to create a computed column using SQL Server Management Studio:
- Run SQL Server Management Studio from Start > Programs > Microsoft SQL Server 2005 > SQL Server Management Studio.

- In the Connect to Server window, click the Connect button.

- In the Microsoft SQL Server Management Studio window, double-click the Databases folder.

- In the Microsoft SQL Server Management Studio window, double-click the required database. Here, the Axle database is being used.

- In the Microsoft SQL Server Management Studio window, double-click the Tables folder.

- In the Microsoft SQL Server Management Studio window, right-click the required table and click Modify.

- Type the name of the new column. Here, Amount is the new column.

- In Column Properties, expand Computed Column Specification. In the Formula box, type the formula. Here, the Price column is multiplied by the Quantity column.

- Go to the File menu and click Save Products to save the modifications in the Products table.

What are the conditions under which a function can be schema bound?
A function can be schema bound only if the following conditions are true:
- The function is a Transact-SQL function.
- The user-defined functions and the views it references are also schema-bound.
- The objects that the function references are referenced using a two-part name.
- The function and the objects it references belong to the same database.
- The user who executed the CREATE FUNCTION statement has REFERENCES permission on the database objects that the function references.
- SCHEMABINDING cannot be specified for functions that reference alias data types or CLR functions.
Friday, November 20, 2009
Wednesday, November 18, 2009
Attitude
Sunday, November 15, 2009
Friday, November 06, 2009
Install multiple versions of IE on your PC
Thursday, November 05, 2009
sql server Xquery Samples
All
author
All
first.name
All
etc....
check below
XPath Examples expressions
XML structure
Key terminology
The material in this section is based on the XML Specification. This is not an exhaustive list of all the constructs which appear in XML; it provides an introduction to the key constructs most often encountered in day-to-day use.
(Unicode) Character
By definition, an XML document is a string of characters. Almost every legal Unicode character may appear in an XML document.
Processor and Application
Software which processes an XML document. It is expected that a processor works in the service of an application. There are certain very specific requirements about what an XML processor must do and not do, but none as to the behavior of the application. The processor (as the specification calls it) is often referred to colloquially as an XML parser.
Markup and Content
The characters which make up an XML document are divided into markup and content. Markup and content may be distinguished by the application of simple syntactic rules. All strings which constitute markup either begin with the character "<" and end with a ">", or begin with the character "&" and end with a ";". Strings of characters which are not markup are content.
Tag
A markup construct that begins with "<" and ends with ">". Tags come in three flavors: start-tags, for example
Element
A logical component of a document which either begins with a start-tag and ends with a matching end-tag, or consists only of an empty-element tag. The characters between the start- and end-tags, if any, are the element's content, and may contain markup, including other elements, which are called child elements. An example of an element is
Attribute
A markup construct consisting of a name/value pair that exists within a start-tag or empty-element tag. In this example, the name of the attribute is "number" and the value is "3":
 An element must not have two attributes with the same name.
An element must not have two attributes with the same name.XML Declaration
XML documents may begin by declaring some information about themselves, as in the following example.
Sql Server Sample
Source
Save Web Page as pdf
Use PDF Download to do whatever you like with PDF files on the Web. Regain control and eliminate browser problems, view PDFs directly in Firefox as HTML, and use the all-new Web-to-PDF toolbar to save and share Web pages as high-quality PDF files.
Install Here
Execise Video DataBase
Learn Correct exercise technique
Exercise videos with tips and instructions
To get the maximum results out of any exercise you should use the correct technique. The best way to learn good technique is one on one, but since we can't get to every gym around the world we've got the next best thing, exercise instruction videos and pictures!
Each video is a demonstration of how to do the exercise using correct technique. There is also additional information, tips, pictures and links on the video pages to help you get the best results using the exercise. If you need help with any of these exercises just ask in the forum.
Source
Wednesday, November 04, 2009
xquery xpath expressions
The axis specifies the direction of movement, relative to the context node. Supported axes in SQL Server 2005 are child, descendant, parent, attribute, self and descendant-or-self.
child : the children of the context node
descendant : all descendants (children, childrens children, ...)
parent : the parent (empty if at the root)
ancestor : all ancestors from the parent to the root
following-sibling : siblings to the right
preceding-sibling : siblings to the left
following : all following nodes in the document, excluding descendants
preceding : all preceding nodes in the document, excluding ancestors
attribute : the attributes of the context node
namespace : namespace declarations in the context node
self : the context node itself
descendant-or-self : the union of descendant and self
Create,View,Edit PDF files Online
Sub Query
The SQL subquery feature lets you use the results of one query as part of another query.
A subquery is a query within a query.
A sub-query is a SQL Server statement embedded inside of another SQL Server statement.
Sub-query execution is dependent upon the nesting level of the query. The execution tree goes from inner-most queries to outer-most queries. The higher nested queries can access the results returned by the lower nested queries.
Paranthesis
- A sub‐query must be enclosed in the parenthesis
- A sub‐query must be put in the right hand of the comparison operator
- A sub‐query cannot contain an ORDER‐BY clause
- A query can contain more than one sub‐query
- Sub Query
- Correlated Sub Query
- Single Row
- Multipe Row
- Multiple Columns
Correlated Sub Query Sample
A correlated sub-query is dependent upon the outer query. The outer query and the sub-query are related typically through a WHERE statement located in the sub-query. The way a correlated sub-query works is when a reference to the outer query is found in the sub-query, the outer query will be executed and the results returned to the sub-query. The sub-query is executed for every row that is selected by the outer query.
____________________________________________________
CREATE TABLE SalesHistory
(
SaleID INT IDENTITY(1,1),
Product VARCHAR(30),
SaleDate SMALLDATETIME,
SalePrice MONEY
)
SELECT SaleDate, Product, SalePrice,
ISNULL(
(
SELECT
SUM(SalePrice)
FROM
SalesHistory sh1
WHERE
Sh1.Product = sh.Product AND
Sh1.SaleID < sh.SaleID
),0) AS RunningTotal
FROM SalesHistory sh
ORDER BY Product, SaleID
____________________________________________________
Saturday, October 31, 2009
Index Seek VS Index scan
SQL Server: Scans and seeks
Scan
 Scans can be performed on any structure (index or heap). Scanning a table means that SQL Server reads all the rows in the table. Only the rows satisfying the search predicate are returned. Scans imply sequential reads that are usually faster than reading each page individually, but the cost of this operation is proportional to the size of the table.
Scans can be performed on any structure (index or heap). Scanning a table means that SQL Server reads all the rows in the table. Only the rows satisfying the search predicate are returned. Scans imply sequential reads that are usually faster than reading each page individually, but the cost of this operation is proportional to the size of the table.The number of logical reads during this operation is the number of pages read during the scan, plus one logical read at each non-leaf level, in case of an index, in order to locate the first row of the table. This operation counts as a scan in the IO statistics.
Seek
 Seeks can only be performed on indexes (clustered or nonclustered). A seek is performed when SQL Server can leverage the ordering of the rows in the index to identify a range of rows in the index that contains all the rows satisfying the search predicate.
Seeks can only be performed on indexes (clustered or nonclustered). A seek is performed when SQL Server can leverage the ordering of the rows in the index to identify a range of rows in the index that contains all the rows satisfying the search predicate.- The seek predicate, such as all the rows within this range satisfy the seek predicate, and all the rows outside of that range don't. Seek predicates are usually predicates on the leftmost columns of the key of an index.
- The residual predicate, such as the search predicate is the conjunction of the seek predicate and the residual predicate. The residual predicate is optional.
Index Scan retrieves all the rows from the table. Index Seek retrieves selective rows from the table.
SEEK is better then SCAN
But there are few scenarios where SCAN operator perform better then SEEK specially when large number of rows are expected to return by operation.
sample
Friday, October 30, 2009
UPDATE STATISTICS
UPDATE STATISTICS updates the indexes on these tables accordingly.
difference between DELETE & TRUNCATE commands
- Delete Removes the rows from a table based on the condition that we provide with a WHERE clause.
- Truncate Actually remove all the rows from a table(i.e there is no where condition on this)
Is faster and uses fewer system and transaction log resources than DELETE.
Deallocates the data pages used to store the table’s data, and only the page deallocations are recorded in the transaction log.
directly delete records without entry in transaction log.
It Can't be rollbacked
But can be rollbacked the following way
SET NOCOUNT ON
GO
INSERT INTO dbo.TEST_TRUNCATE (COL2) VALUES ('TEST TRUNCATE');
GO
BEGIN TRAN
/*Show me the count of the records before truncate*/
SELECT COUNT(*) FROM dbo.TEST_TRUNCATE
TRUNCATE TABLE dbo.TEST_TRUNCATE
/*Show me the count of the records now*/
PRINT 'INSIDE THE TRANSACTION'
SELECT COUNT(*) FROM dbo.TEST_TRUNCATE
/*Rollback now*/
ROLLBACK TRAN
/*Show me the count of the records now*/
PRINT 'OUTSIDE THE TRANSACTION'
SELECT COUNT(*) FROM dbo.TEST_TRUNCATE
______________________________________________________________________________
Delete:
DELETE removes rows one at a time and records an entry in the transaction log for each deleted row.
Can be rollbacked
truncate table the counter used by an identity column for new rows is reset to the seed for the column
If you want to retain the identity counter, use delete statement instead.
You cannot use truncate table on a table referenced by a foreign key constraint
Because truncate table is not logged, it cannot activate a trigger.
Delete statement without a where clause works.
Thursday, October 29, 2009
What's the difference between a primary key and a unique(Candidate) key
- primary key creates a clustered index on the column
- unique creates a nonclustered index by default
- primary key doesn't allow NULLs
- but unique key allows one NULL only.
- you can have multiple unique keys in a table
- can have only one Primary Key
A foreign key is a column (the child collumn) in a table which has a corresponding relationship and a dependency on another collumn (the parent collumn) that is usually in a different table.
Rules of Data Normalization - 2NF
A table in a relational database is said to be in normal form if it satisfies certain constraints. Codd's original work defined three such forms but there are now five generally accepted steps of normalisation.
The most obvious indication that a database is not 2NF is if multiple records in a table might have the exact same value for a column.
To make a database 2NF compliant:
- Identify any fields that do not relate directly to the primary key.
- Create new tables accordingly
- Assign or create new primary keys
- Create the requisite foreign keys indicating the relationships
Rules of Data Normalization - 1NF

Codd states that the "values in the domains on which each relation is defined are required to be atomic with respect to the DBMS.
atomic value are one that "cannot be decomposed into smaller pieces by the DBMS (excluding certain special functions)
- There are no duplicate rows.
- Every row-and-column intersection contains exactly one value from the applicable domain (and nothing else).
* Eliminate duplicative columns from the same table.
* Create separate tables for each group of related data and identify each row with a unique column (the primary key).
A table is in the first normal form if it contains no repeating columns.
single value restriction. The first involves assigning several values to the same attribute:
This should be redefined as a relation with attributes Emp ID, Child, and Gender — but with only one value per attribute. The resulting table should have four rows.
Similarly, each attribute should be separated from the other attributes. Thus, the following is not allowed (or, at least, not encouraged):
Fix this problem by simply creating a relation with Emp ID, Child, and Gender (and four rows).
Derived data are values that can be computed from values in other attributes.
A relation should not contain any derived data. For example, an attribute should not hold the multiplicative product of two other attributes or the grand total of some other attribute.
A table is in 1NF if it adheres to the single value restriction and disallows repeating groups and derived data.
Rules to get to 1NF
1 Break up all attributes so that they are single-valued.
2 Remove all derived data attributes.
3 Define a primary identifier for the relation.
4 Remove all repeating groups. Put them in another relation.
wikipedia source on 1nf
Problems on 1NF
SQL Server Collation
A collation specifies the bit patterns that represent each character and the rules by which characters are sorted and compared.
Sensitive or insensitive to accented characters, also known as extended characters. Accented characters are those characters that have a diacritical mark, such as the German umlaut (ë) or the Spanish tilde (~). For example, accent sensitivity defines whether 'a' is equal or not equal to 'ä'.
* The Unicode data types nchar, nvarchar, and ntext. These data types use the Unicode character representation. Code pages do not apply to these data types.
* The non-Unicode character data types char, varchar, and text. These data types use the character representation scheme defined in a single or double-byte code page.
The easiest way to manage character data in international databases is to always use the Unicode nchar, nvarchar, and ntext data types in place of their non-Unicode equivalents (char, varchar, and text).
Sort Order
A sort order specifies the rules used by SQL Server to interpret, collate, compare, and present character data. For example, a sort order defines whether 'a' is less than, equal to, or greater than 'b'
When you install an instance of SQL Server, you can specify the default collation for that instance during setup. The default collation for the instance also becomes the default collation of the system databases: master, model, tempdb, msdb, and Distribution.
CREATE TABLE MyTable
(PrimaryKey int PRIMARY KEY,
CharCol varchar(10) COLLATE French_CI_AS NOT NULL
)
GO
ALTER TABLE MyTable ALTER COLUMN CharCol
varchar(10)COLLATE Latin1_General_CI_AS NOT NULL
GO
After a collation has been assigned to any object other than a column or database, you cannot change the collation except by dropping and re-creating the object
sample
CDC - Change Data Capture SQL Server 2008
Wednesday, October 28, 2009
Serialization
· Serialization Facts
o Binary serialization can handle graphs with multiple references to the same object;
o XML serialization will turn each reference into a reference to a unique object.
o Binary serialization the entire object state is saved
o while in XML serialization only some of the object data is saved
o
· Serialization Clone:
o Only for serializable objects
o Should be by serialization as it get serialized in web service
Advantages of Binary Serialization
All members, no matter if they are read-only will be serialized.
Greater performance*
Advantages of XML Serialization
Greater flexibility of object sharing and usage (interoperability)
No strict binary dependence
Human readable
T-SQL Query Processing Order
SELECT [...]
FROM [table1]
JOIN [table2]
ON [condition]
WHERE [...]
GROUP BY [...]
HAVING [...]
ORDER BY [...]
What is the difference between varchar and nvarchar
The main reason for preferring nvarchar over varchar would be internationalization (i.e. storing strings in other languages).
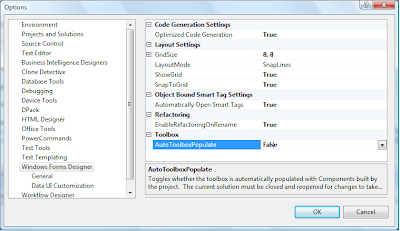
speed up the visual studio disable toolbox controls load
2) Click the Windows Forms Designer Node
3) Disable AutoToolboxPopulate (Make it false)
Close Visual Studio
Restart it
If you include a custom built control in your project, it will not show up automatically on the toolbox
What are the difference between clustered and a non‐clustered index?
SQL Server data structures
Pages
Structure of a table: heaps and clustered tables
Heaps
Clustered tables
Leaf level:
The leaf level is the data of the table. It is composed of data pages. They store all the columns of the table for every row of the table.
Non-leaf levels:
The non-leaf levels are composed of index pages.
At every non-leaf level, each index row corresponds to a page in the next level. Each index row in every index page contains two things: the index key value, which is the first key value of the corresponding page in the next level of the index, and a 6 bytes page pointer to that corresponding page.
Nonclustered indexes
Leaf level:
In a nonclustered index, the leaf level is composed of index pages instead of data pages. Each index row in the leaf level of a nonclustered index contains a nonclustered key value along with a row locator that points to the corresponding data row in the actual table structure (heap or clustered table).
If the associated table is a heap, the row locator is an 8 bytes row ID. If the table is a clustered table, the row locator is the clustering key identifying the row.
Non-leaf levels:
The non-leaf levels of a nonclustered index are used for navigation identically as in a clustered index.
Covered columns
- No indexes
- A clustered index
- A clustered index and many nonclustered indexes
- A nonclustered index
- Many nonclustered indexes
INDEX index_name
ON table (column [ASC
DESC] [ ,...n ] )
[WITH {IGNORE_DUP_KEY
DROP_EXISTING
SORT_IN_TEMPDB}]
[ON filegroup ]
CREATE TABLE dummytable1 (
empid INT,
empname VARCHAR(700))
INSERT INTO dummytable1
VALUES (4,
Replicate('d',700))
GO
INSERT INTO dummytable1
VALUES (6,
Replicate('f',700))
GO
INSERT INTO dummytable1
VALUES (1,
Replicate('a',700))
GO
INSERT INTO dummytable1
VALUES (3,
Replicate('c',700))
GO
SELECT empid
FROM dummytable1
GO
CREATE CLUSTERED INDEX ix_dummytable ON dbo.dummytable1 (
empid)
SELECT empid
FROM dummytable1
GO
CREATE NONCLUSTERED INDEX ix_dummytable1 ON dbo.dummytable1 (
empname)
GO
SELECT *
FROM dummytable1
WHERE empname LIKE '%a%'
AND empid = 1
GO
The Clustered/Non Clustered index can be enabled disabled
primary key creates a clustered index on the column, where as unique key creates a nonclustered index by default.
Sunday, October 11, 2009
Friday, October 02, 2009
Trace Indian Mobile Location & Operator
Searches across Indian mobile number details...
Updated Regularly
This is a good websit. you can know some phone no. Location & Operator
Self-Massage for Athletes
Massage away muscle pain and soreness
Turn your hands into powerful pain relievers. Are you aching in the places where you used to play? Join the revolution and feel better fast
Friday, September 11, 2009
Watch Vocabular Videos Studying vocabulary or just want to improve your vocabulary? This ‘video dictionary’ is indispensable!
http://www.wordahead.com/WordList/tabid/71/Default.aspx
Tuesday, September 01, 2009
OpenDns Stay Secured
start
OpenDNS Server Ip Address
208.67.222.222 and 208.67.220.220.
Saturday, August 08, 2009
Effective Communication
In the case of IT, we primarily deal with American and UK clients. It is useful to know how English language works with them.
Some of us may hesitate to speak to the client, because we are not confident. ‘Practice makes you confident’
“Practice these tips…….”
PowerPoint
Incredible!!!New initiative of Govt of India ............ Very Informative - read, save & pass on
Government of India has an online Grievance forum at http://www.pgportal.gov.in
Can you imagine this is happening in INDIA ?
The govt. wants people to use this tool to highlight the problems they faced while dealing with Government officials or departments like (all hyperlinks given below links to respective dept/office site)
Many of us say that these things don't work in India .
Couple of months back, the Faridabad Municipal Corporation laid new roads in the area and the residents were very happy about it. But two weeks later, BSNL dug up the newly laid roads to install new cables which annoyed all the residents. A resident used the above listed grievance forum to highlight his concern. To his surprise, BSNL and Municipal Corporation of Faridabad were served a show cause notice and the guy received a copy of the notice in one week. Government has asked the FMC and BSNL about the goof up as it's clear that both the government departments were not in sync at all.
So use this grievance forum and educate others who don't know about this facility.
This way we can at least raise our concerns instead of just talking about the 'System' in India .
Invite your friends to contribute for many such happenings.
PLEASE SPREAD THIS MESSAGE IF U WANT OUR INDIA TO HAVE A BETTER TOMORROW
Popular Posts
|















.gif)